The 7 Best Smart Card Readers

This wiki has been updated 39 times since it was first published in March of 2016. Smart cards are widely acknowledged as one of the most secure and reliable forms of electronic identification, and are beginning to attain widespread use in a variety of civil and military applications. But to get at their data, you'll need one of these readers. Some of our selections offer additional functionality with their ability to read multiple formats of digital memory storage. When users buy our independently chosen editorial selections, we may earn commissions to help fund the Wiki.
Editor's Notes
March 30, 2021:
On its fundamental level, CAC smart card technology has not changed in years, and it almost certainly won't change significantly anytime soon. For that reason, the only recent change to this Wiki was the removal of the Gemalto IDBridge, which is now difficult to find and offers no tangible benefits compared to other options. Given their simplicity, these devices come down mostly to dependability, which all of our recommendations offer, and USA-sourced materials. That last part is important to many governmental offices and contractors, and as such, those institutions should look to the IOgear GSR205 for an American-made security solution.
Some of these models also support EMV payment processing, however, if you need to accept payments on a regular basis, we high recommend getting a dedicated credit card reader. For contactless smart cards that have more highly-powered RF circuits inside them, you'll need a specialized proximity card reader.
February 14, 2020:
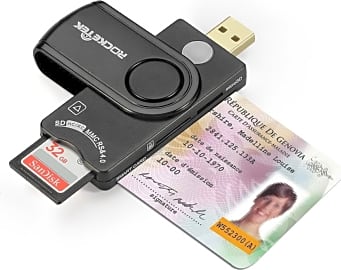
There's not a ton differentiating these from each other, but you'll still need to make sure you get the right one. Right off the bat, the IOgear GSR205 is one of the best choices because, unlike many, it's compliant with TAA regulations that require many government offices to use devices produced mainly in the USA. The Identiv SCR3500 Smartfold and Identiv SCR-3310 are also excellent options made by one of the leaders in secure access components. There's also the Daoker SCR653C, which, like the IOgear, has a USB-C connector for use with modern smartphones and notebook computers. The Daoker has the added benefit of built-in SD card readers, as does the Rocketek SCR10, which also happens to be among the most compact.
If portability isn't your primary concern, check out the HID Omnikey, which is highly reliable but slightly bulkier than others. And if you definitely don't need to take it anywhere, the Dell SK-3205 keyboard features a permanently integrated reader.
Also note that these products are not designed to take payment cards or communicate with NFC devices. To do those, you'll need a credit card reader or proximity card reader
Special Honors
Thursby PKard Reader If you need one that has a Lightning connector and works perfectly with iOS, the PKard Reader is one of the few options available to you. It's a bit pricey, but if you need to access a secure iPad or iPhone, it's likely worth the investment. thursby.com
Identiv iAuthenitcate 2.0 From one of the most popular manufacturers of secure access hardware, this is one of just a handful of options that's compatible with most iPhones and iPads. It's highly ruggedized and built so the reader sits behind the phone or tablet for maximum convenience. identiv.com
Digital Safety Of The Highest Degree
Data like proprietary business plans, financial accounts, intelligence files, and troves of personal documents live on the overarching and sometimes mysterious cloud.
The 21st century is a decidedly digital world. Data like proprietary business plans, financial accounts, intelligence files, and troves of personal documents live on the overarching and sometimes mysterious cloud. Businesses and consumers are adopting paperless systems for the ease of record-keeping and identity confirmation. We're far past the times when one number could be used to secure the professional and financial standing of each individual, and if current events are any indication, encryption and authentification will only become more pressing concerns as technology and its pervasiveness advance.
What does this mean for people with jobs in government, finance, medical research, security, and other sensitive industries? There are millions of Americans working in these sectors, and the last thing any of them need is an imposter stealing their identity and engaging in fraud. To keep everyone honest, a good place to start is with a system actually made popular by the U.S. Department of Defense.
One thing many people don't realize is that even the system adopted as the standard for digital transmission across the internet itself was designed by the Department of Defense. The protocol used to uphold the worldwide web is sometimes referred to as the DoD model. And, let's be honest, the U.S. government has access to some of the top scientists and economically influential figures in the world; if TCP/IP is good enough for them, it stands to reason that it's good enough for the public. And maybe, just maybe, there's additional technology available from those researchers that can aid other industries in their quest for personal and data security.
That technology is real, and it is called the smart card: a widely popular method for in-person and remote access to high-security facilities and encrypted data. Every major credit card company in the world, as well as most cell phone manufacturers, use smart card technology for storing your personal information, documents, or media, meaning a piece of this important advancement may be in your pocket right now.
How Smart Are They?
To be clear, these chips can't help you with your homework or file your taxes for you. They're not quite that smart yet. But they do have incredible functionality nonetheless. For starters, it's easy to recognize a smart card. The most common one you'll see on a regular basis is the credit card itself, whether it's a Mastercard, Visa, or any other. The U.S. mandated that all payment cards contain a smart chip beginning in 2014, while the E.U. has had the system in place for longer. Cards used for personal identification and access to secure systems are sized the same as a credit card and known as a common access card, or CAC. Most will have an easily-recognizable set of metal contacts that denote it as a smart unit. These contacts serve as the conduit between the secure filesystem embedded in the card and the reader connected to your computer, security system, or payment network.
The most common one you'll see on a regular basis is the credit card itself, whether it's a Mastercard, Visa, or any other.
Another type does not use physical metal contacts, but rather transmits data through the air using RF technology. This makes it easy for employees to access secured facilities throughout the workday. Some cards use both physical and wireless connections. These hybrids often have separate data storage and encryption for either connection, while dual-interface models share the same internal storage and instructions no matter which connection is used. Most smart cards also include embedded instructions on how to translate their secure data for transmission over USB cable, an important feature for many users. This enables their use with personal computer systems and mobile-based point-of-sale transactions.
Smart chips are all constructed according to a pair of international standards (ISO/IEC 14443 and 7816, for those keeping score), meaning they should all be compatible with systems used in every country around the world. They're powered by the energy from the reader itself, so there's no need to worry about battery levels. Traditional chips draw power through their contacts, while RF cards draw power wirelessly when they're within a few inches of the receiver.
And How Do I Read Them?
We've established that a large number of adults will use a smart card at some time in their lives, even if it's just to buy groceries. But millions of people work directly for or contract with the government and various other highly sensitive organizations. Some of these employees will need remote access to secure computer systems. Some organizations even require individually secured logins at on-the-job computers as an added measure of security. And the Department of Defense isn't always chomping at the bit to supply every single contractor with all the peripherals they need to do their job. Luckily, there's no shortage of effective and inexpensive smart card readers available to the general public.
No matter how you use it, you can be sure this technology is among the most secure available today.
The vast majority of these readers will connect to your desktop or laptop's USB port. Some helpful models can connect directly to a micro-USB port, so you can accept payment cards for your small business using only your smartphone. Some specialized designs plug into a laptop's ExpressCard slot and are slimmer, faster, and lighter than those using a USB dongle. They can also come integrated directly into a quality keyboard, which is perfect for outfitting an office with multiple secured access points.
When you do decide on one of these low-cost options, double-check to make sure it will work perfectly with your smart card. A majority of identity-confirming cards are sized similar to the common credit card, so if you also want to access smaller smart cards such as your phone's SIM card, you'll need to get a reader that accepts multiple formats. And if you'll be using the reader to accept electronic payments from customers, be sure that your choice is EMV-certified, and in compliance with international standards. No matter how you use it, you can be sure this technology is among the most secure available today.